Web Application Security in the Cloud-First Era
In 2025, most applications no longer live on physical servers tucked away in an office corner. They run in the cloud — scalable, accessible, modern. But with flexibility comes an uncomfortable question: who’s responsible for security? In the cloud-first era, we take on more than we realize. Let’s look at where things can go wrong and how to avoid critical security mistakes in web app development.
1. Classic attacks are still dangerous
XSS, SQL injection, CSRF — sound like “old problems”? Don’t be fooled. OWASP 2025 stats show these vulnerabilities are still among the most exploited. Our code — not the cloud platform — is responsible for them.
What to do:
- Validate and sanitize user input on the server, not just in the frontend
- Use frameworks with built-in protections (e.g., Laravel, Next.js, Symfony)
- Scan your code regularly with automated tools (OWASP ZAP, SonarQube)
2. Understand the shared responsibility model
When using AWS, GCP, or Azure, you’re not off the hook. The cloud provider secures the infrastructure, but everything you build on top (apps, configs, code, databases) is your responsibility.
Remember:
- A public S3 bucket or an open container port = a wide-open door for attackers
- Password, token, and API key management is entirely up to you
- General rule: “The cloud gives you a castle, but the developer locks the doors”
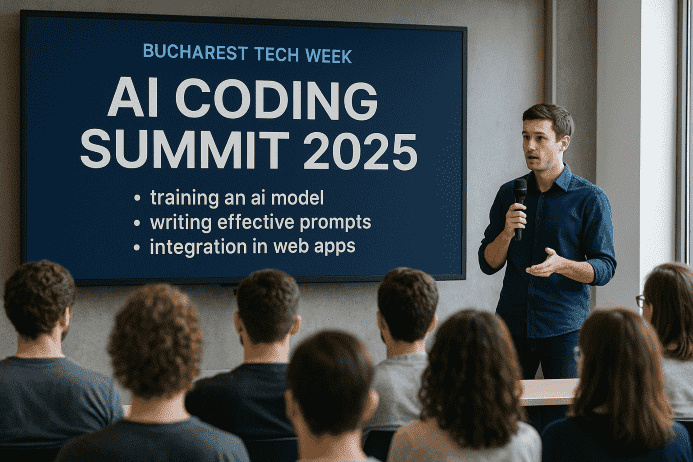
3. Integrate DevSecOps — even in small teams
Security must be part of the development cycle, not a separate step after delivery. That’s the DevSecOps philosophy: development + security + operations, with continuous feedback.
How to start:
- Add automated checks to your pipeline (GitHub Actions, GitLab CI)
- Set code rules and permission limits directly in the repo
- Include regular threat modeling sessions with your team
4. Real-world measures used in IB-Media projects
At IB-Media, we actively protect our clients’ applications. Beyond code audits and QA, we use:
- WAF (Web Application Firewall) configured per client
- Incremental backups with off-site storage
- Automated SSL via Let’s Encrypt and enforced HTTPS
- Manual review before every major deploy
Security isn’t a product — it’s a process. And in the cloud, that process must be continuous and transparent.

Be the first to comment!